Prerequisites:
OCI Network Firewall – Concepts and Deployment
OCI Network Firewall – NAT Gateway use case
OCI Network Firewall – Hub and Spoke traffic inspection
The forth blog dedicated to the OCI NFW is focused on the integration between the OCI NFW and the OCI LBaaS. The setup is required mostly because it will offer a rock-solid security architecture by combining the NFW capabilities with the LBaaS WAF. In this blog we will not discuss the WAF functionality, we will just analyze the integration part and the NFW configuration.
The networking topology used:
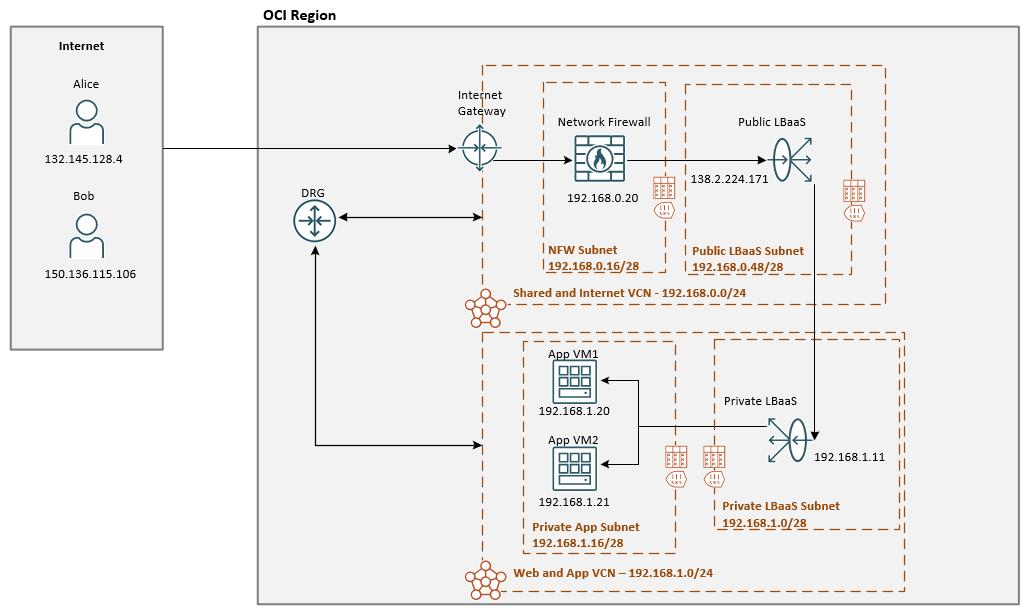
We have two hosts on the Internet trying to initiate the connections, generally called Alice and Bob. The initiated connection from Alice to the public IP address of the public LBaaS at 138.2.224.171 in the Shared and Internet VCN through the NFW should be allowed. On the other hand, the Bob’s initiated connection needs to be rejected by the NFW.
The Web and App VCN will contains the backed servers which are front ended by a private LBaaS at 192.168.1.11.
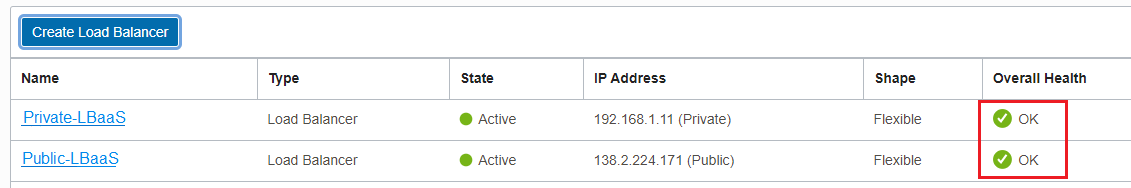
In the first phase we need to make sure the health-check between the Public LBaaS and Private LBaaS and between private LBaaS and the back-end servers is in good condition:
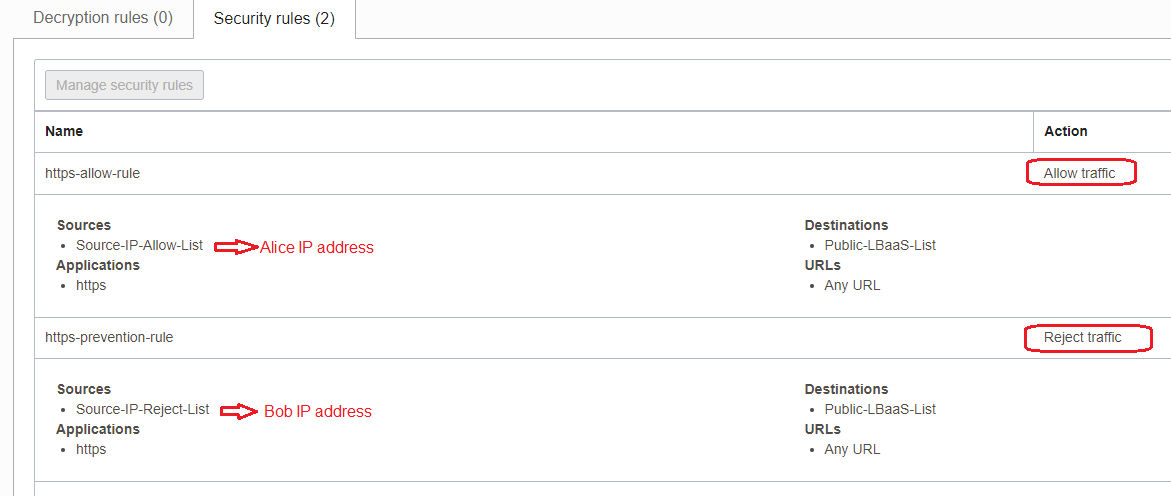
As we already learned from our previous NFW blogs, the two policies that will accomplish the above scope are listed below:
After the rules are in place let’s just test the connection and verify the NFW logs:
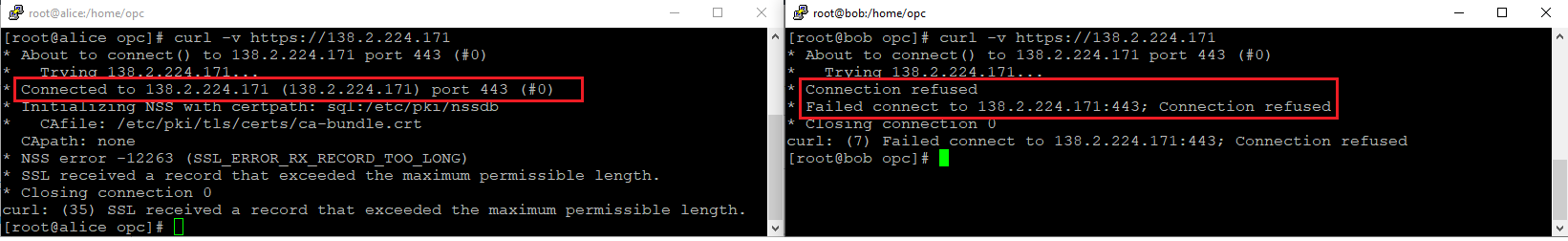
Alice – accepted, Bob – refused.
NFW traffic log analyze:
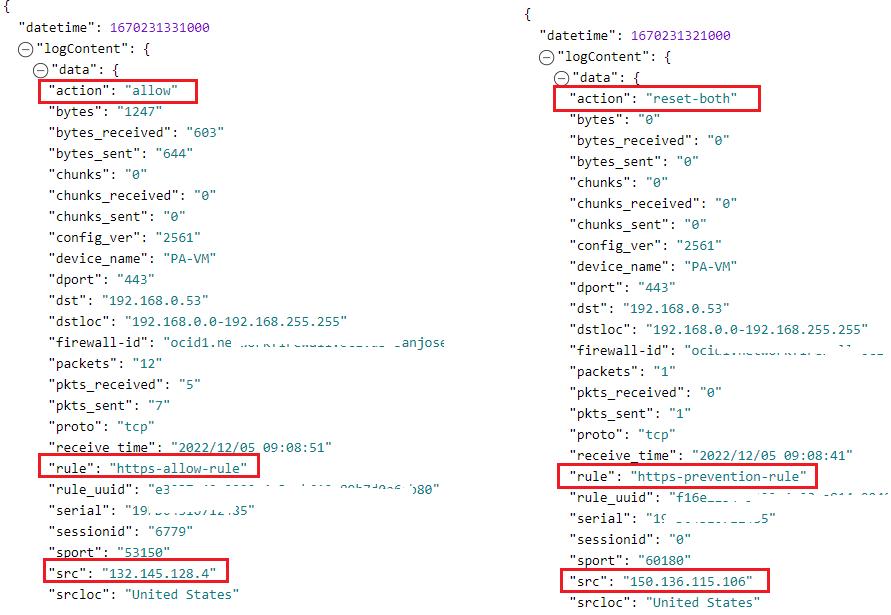
Public LBaaS log analyze:
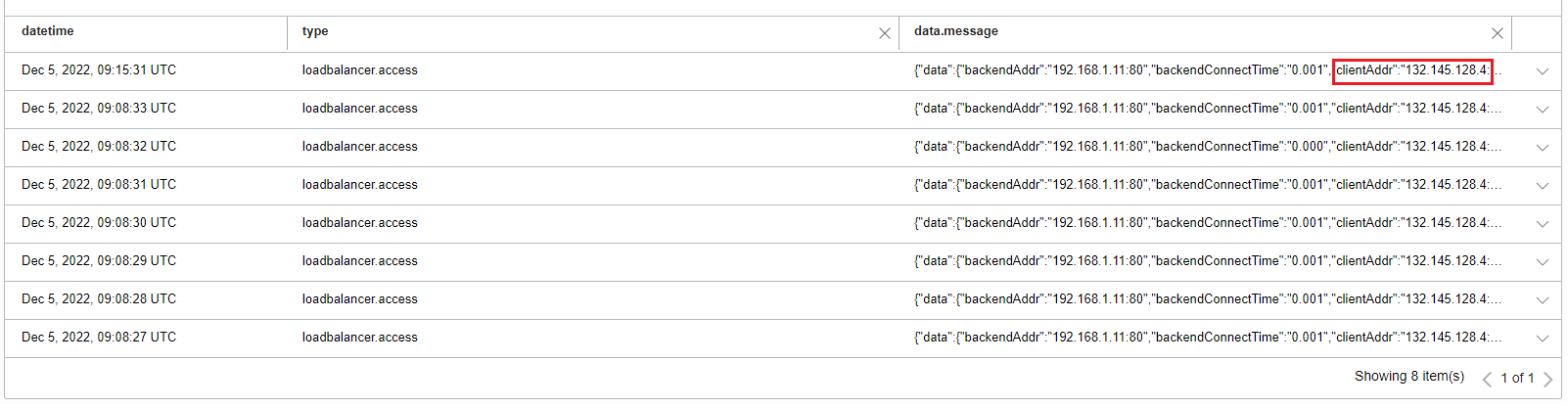
As we can from the above logs, only Alice is able to access the OCI App VMs behind the private LBaaS.
