Introduction
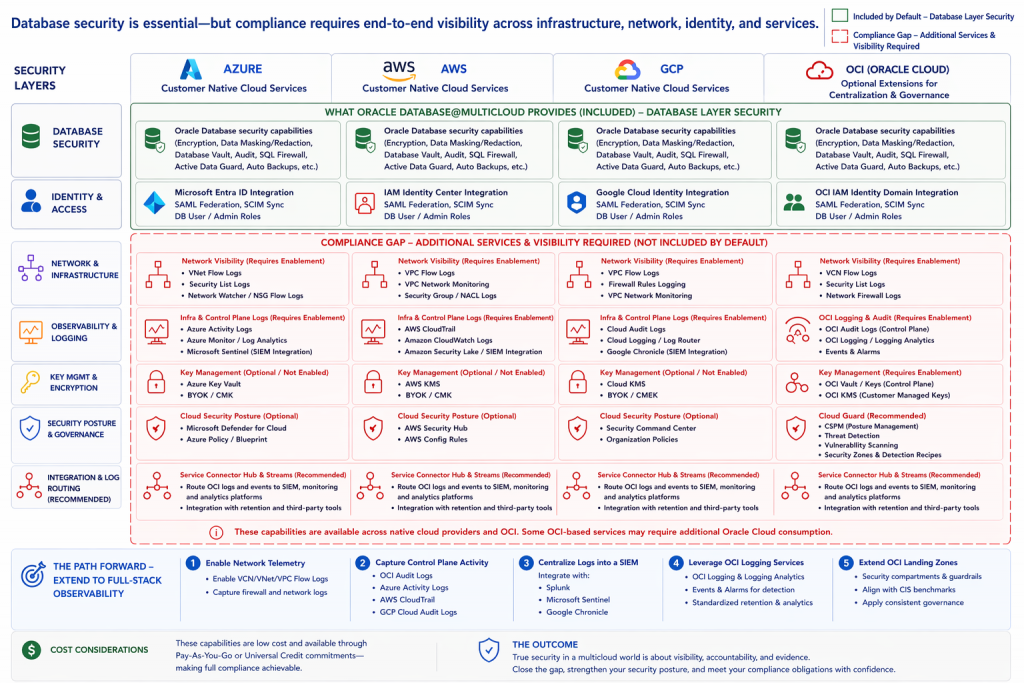
Oracle Database@Multicloud delivers a strong security foundation, especially at the database layer. Capabilities like Deep Data Security, Database Vault, Data Safe, encryption, and unified auditing help ensure that sensitive data is well protected.
But in today’s regulatory environment, securing the database is only part of the requirement.
Compliance frameworks expect organizations to demonstrate end-to-end visibility across the entire environment from infrastructure and network activity to identity and access events. That’s where many multicloud deployments need to evolve.
A strong foundation at the database layer
Oracle Database@Multicloud provides a robust set of built-in protections:
- Encryption, masking, and redaction
- Privileged access controls with Database Vault
- Auditing and threat detection with SQL Firewall
- Integrated backup and recovery
- Deep Data Security
These capabilities create a secure and resilient data platform. From a database perspective, the controls are strong and well understood by both DBAs and security teams.
With Oracle Database 26ai, this foundation is extended further with capabilities like Deep Data Security.
Organizations can now:
- Discover and classify sensitive data automatically
- Apply policy-driven protections based on data sensitivity
- Monitor and control access to critical data in real time
This represents a shift from simply securing the database to understanding and protecting the data itself.
Where the gap emerges
While the database layer is well secured, compliance requirements extend beyond it.
Organizations also need visibility into:
- Network traffic patterns
- Infrastructure and API activity
- Identity and access changes
- Cross-environment security events
These capabilities exist across Azure, AWS, GCP, and OCI. However, they are not always enabled, integrated, or centralized by default.
This is where the gap shows up not in the availability of features, but in how they are brought together.
Understanding the multicloud reality
Across Azure, AWS, and GCP environments, a consistent pattern emerges:
- The database layer is hardened and well managed
- Identity is federated and controlled
- Infrastructure logs, flow logs, and monitoring are handled separately
At the same time, OCI provides additional capabilities—such as logging, audit, and security posture services—that can be used to extend and centralize visibility.
The result is a split model:
- Native cloud services provide core telemetry
- OCI services can extend, aggregate, and govern that telemetry
Why this matters for compliance
Frameworks such as PCI-DSS, HIPAA, FedRAMP, and ISO 27001 require:
- End-to-end auditability
- Centralized logging
- Correlation of events across layers
It’s not enough to secure the data—you must also be able to demonstrate:
- Where access originated
- What changes were made
- How activity is monitored and tracked across systems
Without this level of visibility, organizations can face challenges during audits—even when strong security controls are in place.
What an audit actually looks like
Consider a common scenario.
An auditor asks for evidence of a privileged user accessing sensitive data.
From the database perspective, the organization can show:
- The login
- The queries executed
- The audit trail
But the next questions go further:
- Where did the connection originate?
- Was it from an approved network location?
- Were there related infrastructure or identity changes?
- Can this activity be correlated across systems?
Answering these questions requires more than database logs.
It requires:
- Network telemetry (flow logs)
- Control plane visibility (audit logs)
- Centralized monitoring across environments
If those pieces aren’t in place, the challenge becomes one of proof—not protection.
Extending security to full-stack visibility
Closing this gap doesn’t require a major redesign, but it does require a deliberate approach.
Start with network visibility
Enable VCN flow logs across OCI and the underlying hyperscaler environments so you can see how traffic is moving.
Capture control plane activity
Make sure audit logging is enabled everywhere—OCI Audit Logs, Azure Activity Logs, AWS CloudTrail, and GCP Cloud Audit Logs.
Centralize and correlate logs
Logs spread across multiple clouds don’t help during an audit. Bring them together into a SIEM such as Splunk, Microsoft Sentinel, or Google Chronicle.
Use OCI to extend and standardize visibility
OCI Logging, Logging Analytics, Events, and Alarms can provide a consistent layer for monitoring and detection. Services like OCI Service Connector Hub and Streaming allow logs and events to be routed to SIEM platforms and analytics tools in a scalable way.
Add security posture and governance
Services like Cloud Guard can help with cloud security posture management, threat detection, and continuous monitoring across environments.
Extend your landing zone
Treat logging, monitoring, and governance as part of the base architecture. Use compartments, guardrails, and CIS-aligned patterns to standardize deployments.
A practical and flexible approach
One of the advantages of this model is flexibility.
Many of the required capabilities already exist within the customer’s native cloud environment. OCI services can then be used where it makes sense to centralize, enrich, or extend visibility.
These services are typically:
- Consumption-based
- Low cost
- Available through Pay-As-You-Go or Universal Credit models
In most cases, the challenge is not cost—it’s awareness and design.
The takeaway
Oracle Database@Multicloud provides a secure and resilient foundation for protecting data.
But compliance requires more than strong database controls.
It requires the ability to demonstrate, trace, and verify activity across the entire environment.
Final thought
In a multicloud world, security is no longer defined solely by controls at the data layer.
It is defined by visibility, accountability, and the ability to prove that controls are working as intended.
Organizations that extend their architecture to include infrastructure logging, network telemetry, centralized monitoring, and security posture management will be better positioned—not just for compliance, but for stronger overall security.