Several days ago I received a request to hide the source IPv4 address when the traffic is sent from one of the spokes VCNs to the On-premises network. How easy is to hide it and what are the costs associated? Let’s see.
Networking Topology
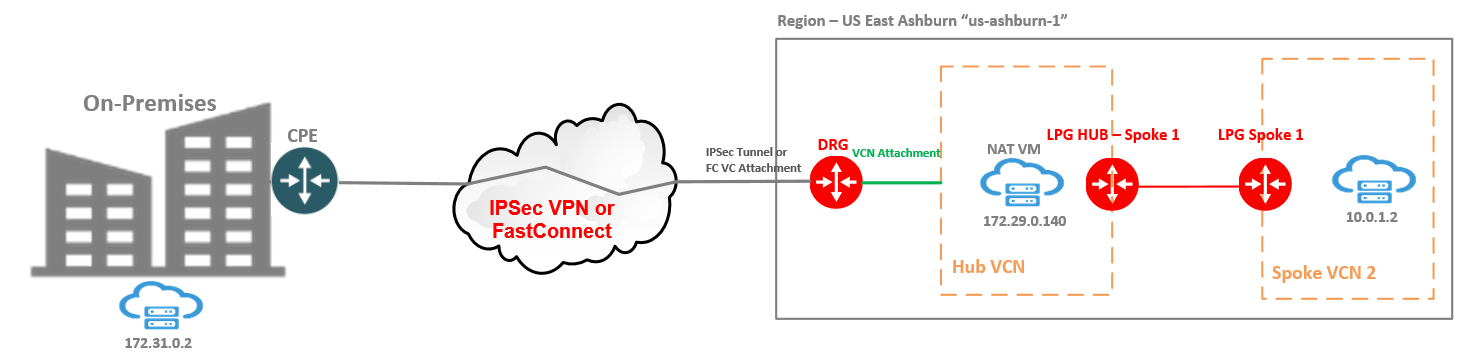
Our OCI VM from Spoke 2 at 10.0.1.2 needs to access 172.31.0.2 with the request that at the 172.31.0.2 the source IP address of the traffic needs to be172.29.0.140, which is assigned to the NAT VM. Yes, your guess is right, we will use a NAT VM in between and we will translate the source IPv4 address from 10.0.1.2 to 172.29.0.140. In this case, all the traffic originated by the 10.0.1.2 toward 172.31.0.2 needs to flow through the NAT VM.
In this example the connectivity between On-Premises network and OCI is achieved by using an IPSec tunnel with BGP for route advertisement.
Network and VM Configuration
1. LPG HUB – Spoke 1 route table configuration:
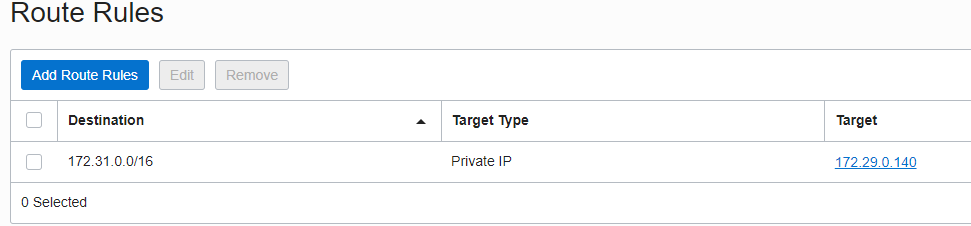
The scope of the above route entry is to make sure the traffic toward 172.31.0.0/16 network is intercepted by the NAT VM.
On the NAT VM interface, please make sure the “Skip/source/destination check” option is enabled.
2. On the NAT VM, the following configuration is necessary, perform the configuration with root access:
echo 1 > /proc/sys/net/ipv4/ip_forward
iptables -P INPUT ACCEPT
iptables -P FORWARD ACCEPT
iptables -P OUTPUT ACCEPT
iptables -t nat -A POSTROUTING -o ens3 -j MASQUERADE
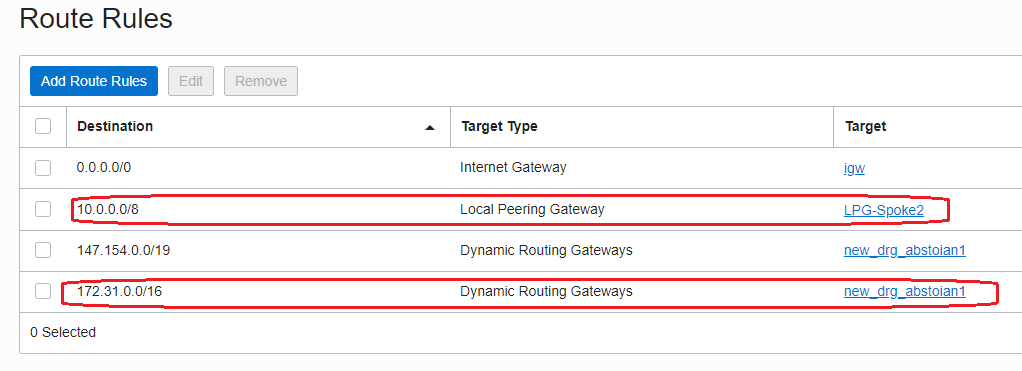
3. The route table associated with the subnet where the NAT VM VNIC is located, needs to send the traffic to the DRG as a next-hop for 172.31.0.0/16 destination and to the HUB-LPG for 10.0.1.0/24 destination:
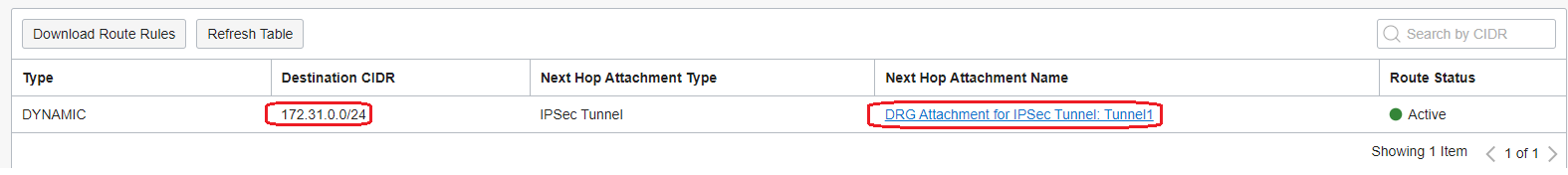
4. The Route Table for the HUB VCN attachment needs to have a route to 172.31.0.0/16 destination with the IPSec tunnel attachment as a next-hop:
Traffic Testing
For the test to be as complete as possible, we will send ICMP traffic from 10.0.1.2 to 172.31.0.2 and we analyze if the traffic arrives at the destination having the source IP address of 172.29.0.140 and not 10.0.1.2.
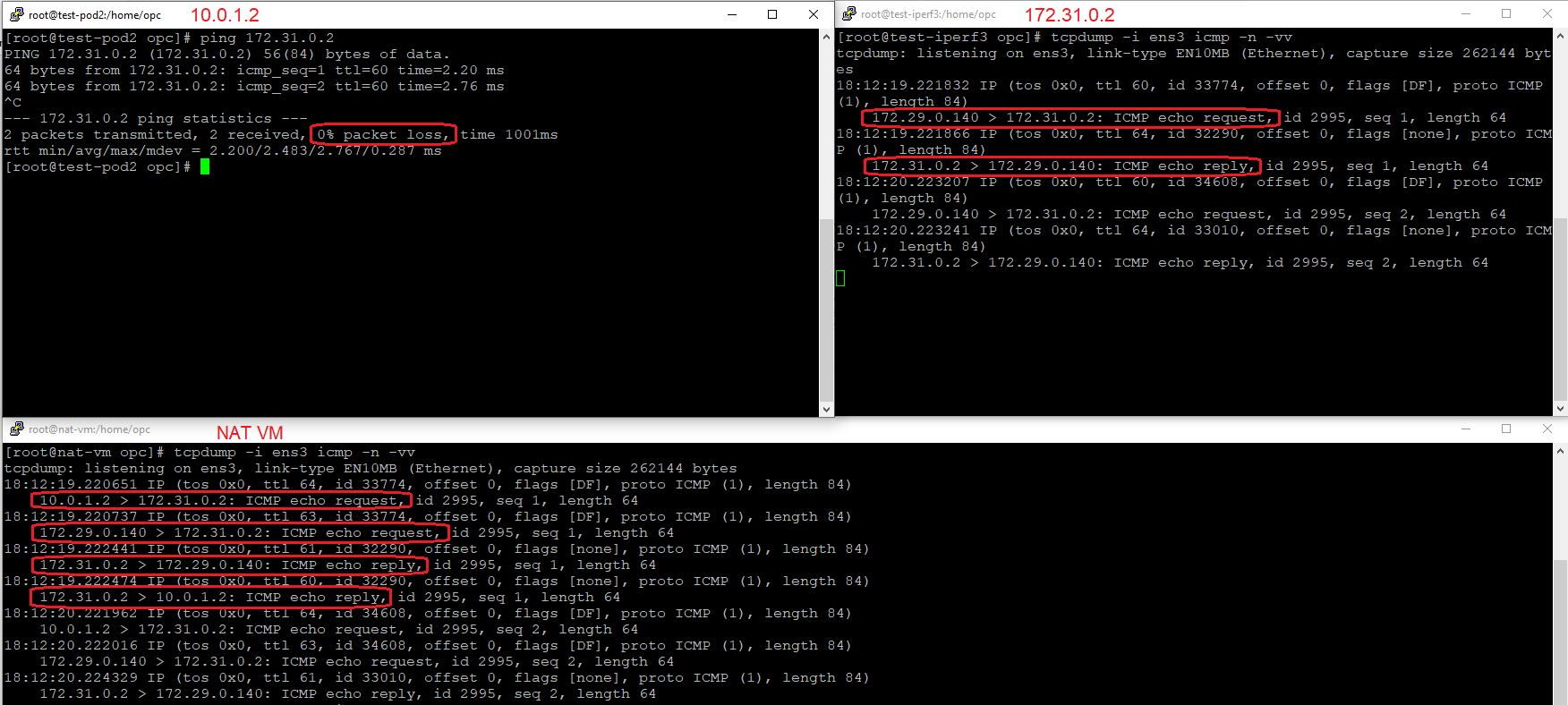
As we expected, the source IP address of the traffic reaching the destination On-Premises is 172.29.0.140 and not 10.0.1.2, so, we hide the real source IPv4 address of the traffic.
Let’s check the NAT table on the NAT VM and confirm our source NAT counters are increasing:
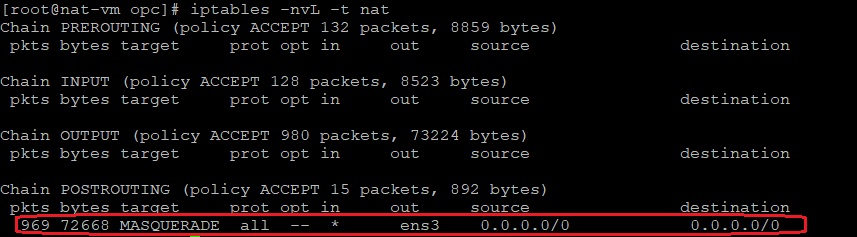
The NAT table confirms the counters are increasing and are alligned with the packet capture on the NAT VM.
In this way, the source IP address was hidden in front of the On-Premises host.
