In today’s threat landscape, the question security leaders increasingly ask is no longer “Is the cloud secure?” but rather:
“How much trust must we place in the cloud provider?”
As CISOs, we are responsible for protecting sensitive data, intellectual property, and systems that often operate at national or industry scale. That responsibility requires us to assume that risk can exist anywhere, including within the infrastructure itself.
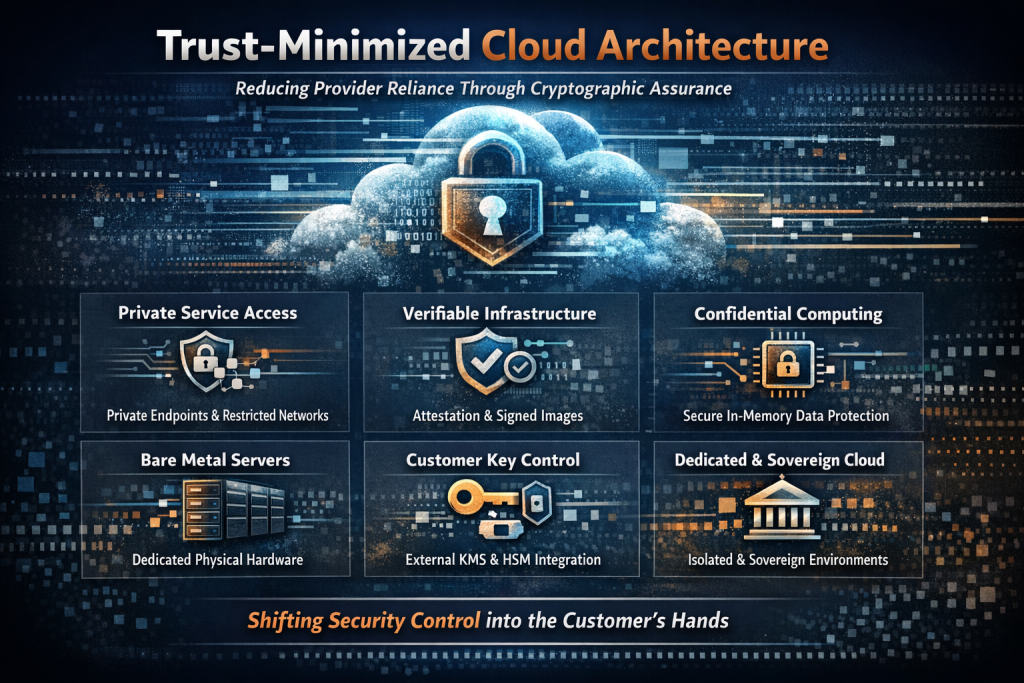
Modern cloud security strategy therefore focuses on minimizing implicit trust, reducing insider risk, and placing meaningful security control directly in the hands of the customer.
From my perspective, the most resilient cloud architectures are those where security assurance is derived from verifiable controls such as cryptography, strong isolation, and customer-defined governance, rather than relying solely on provider assurances or operational processes.
Understanding the shared responsibility model is fundamental to achieving this objective.
Cloud providers secure the underlying infrastructure, but customers must deliberately architect their environments to take advantage of the security controls available within the platform. The most resilient cloud environments intentionally shift key security decision points, including identity, encryption, workload protection, and access governance, into the customer tenancy.
Within Oracle Cloud Infrastructure (OCI), several architectural capabilities support this trust-minimized model.
Minimal Control and Data Plane Exposure
(Private Endpoints and Customer-Managed Service Access)
OCI enables organizations to significantly reduce their external attack surface by restricting cloud service access to private networks and customer-controlled identity policies.
Through capabilities such as private service endpoints, private networking, and tightly scoped network access controls, organizations can prevent management interfaces and service endpoints from being broadly exposed to the public internet.
Using OCI Identity and Access Management (IAM) and Identity Domains, organizations can enforce:
• Strong authentication
• Granular authorization policies
• Strictly controlled administrative access paths
This ensures that access to critical management planes is governed by customer-defined security policy rather than relying on implicit trust in the cloud provider’s operational boundaries.
The result is an architecture where management and service interactions remain within controlled and trusted network paths.
Transparent and Verifiable Infrastructure
(Attestation and Signed Images)
Security in modern cloud environments increasingly depends on verifiable trust rather than assumed trust.
OCI supports infrastructure verification mechanisms such as:
• Image Signing – Ensures that only trusted, cryptographically signed images are deployed to compute environments, allowing customers to verify image integrity and provenance before workloads are launched.
• Cryptographic Attestation – Provides verifiable proof that infrastructure components and workloads are running in a trusted state, enabling customers to validate platform integrity and enforce security policies based on attested measurements.
These capabilities allow organizations to validate the integrity of system images and workloads before execution, ensuring that only verified and trusted workloads are deployed.
Through these mechanisms, trust is derived from cryptographic proof, strengthening an organization’s ability to detect tampering and validate workload integrity throughout the deployment lifecycle.
Confidential Computing
Confidential computing extends data protection beyond traditional encryption states by protecting data while it is actively being processed in memory.
By leveraging hardware-based trusted execution environments (TEEs), OCI enables sensitive workloads to run securely even in infrastructure environments that may otherwise be considered partially untrusted.
This capability protects sensitive data from inspection, including by privileged administrators, and represents a significant advancement in securing highly sensitive workloads.
For organizations operating in regulated industries, financial services, healthcare, or national infrastructure, confidential computing provides an additional layer of assurance that sensitive data remains protected throughout its lifecycle.
Bare Metal Infrastructure Control
(OCI Bare Metal Compute)
Another important architectural capability for minimizing provider trust is the availability of bare metal infrastructure.
Unlike traditional virtualized cloud environments where multiple customers share a hypervisor layer managed by the cloud provider, OCI Bare Metal Compute instances provide customers with direct access to dedicated physical server hardware.
This architecture:
• Removes the hypervisor layer from the trust boundary
• Provides full administrative control over the operating system
• Allows direct implementation of custom security controls
With OCI Bare Metal, organizations maintain control of:
• Kernel configuration
• Security tooling
• Host-based monitoring
• Intrusion detection
• Patch management strategies
This level of control enables security teams to implement custom hardening standards, host-based security controls, and specialized workload isolation techniques that may not be possible in more abstracted cloud environments.
For high-performance workloads, regulated industries, and security-sensitive environments, this architecture significantly reduces the number of intermediary control layers between the customer and the hardware executing their workloads.
From a security architecture perspective, bare metal infrastructure reduces the operational trust surface while preserving the elasticity and automation benefits of cloud computing.
Customer-Controlled Encryption Keys
(OCI Vault with External KMS or HSM Integration)
Strong cryptographic control is a cornerstone of modern cloud security architecture.
OCI enables organizations to maintain ownership of their encryption keys through OCI Vault, including integration with external key management systems or hardware security modules (HSMs).
By maintaining control over key generation, storage, and lifecycle management, organizations can ensure that data confidentiality remains under their direct authority.
This architecture reduces insider risk and strengthens regulatory compliance by ensuring that data protection does not depend solely on cloud provider operational controls.
Dedicated and Isolated Tenancy
(OCI Dedicated Regions and Sovereign Cloud)
For organizations requiring the highest levels of operational control and data sovereignty, OCI provides Dedicated Regions and Sovereign Cloud deployments.
These environments enable infrastructure deployments that are:
• Dedicated to a single organization or jurisdiction
• Aligned with national regulatory frameworks
• Architected for strict operational isolation
This model shifts additional elements of operational control toward the customer while supporting sovereignty, regulatory compliance, and national security requirements.
Strategic Takeaway for Security Leaders
For CISOs, the critical shift in modern cloud security architecture is moving from provider trust to verifiable control.
By leveraging capabilities such as confidential computing, customer-managed encryption keys, strong identity governance, private networking, bare metal infrastructure, and dedicated tenancy, organizations can design cloud environments where security assurance is grounded in architecture and cryptographic verification rather than operational trust alone.
When implemented correctly, these controls allow enterprises to:
• Maintain cryptographic authority over their data
• Enforce strict identity governance
• Protect sensitive workloads throughout their lifecycle at rest, in transit, and increasingly in use
The strongest cloud security architectures are those where trust is intentionally shifted toward the customer through architecture, cryptography, and governance.